Autodesk is hosting malicious PDF files that lead phishing attack victims to have their Microsoft login credentials stolen.
The elaborate phishing campaign behind these attacks is much more convincing than normal, as it uses compromised email accounts to find and attack new targets. These accounts are used to send phishing emails to existing contacts, using the sender’s real email signature footer.
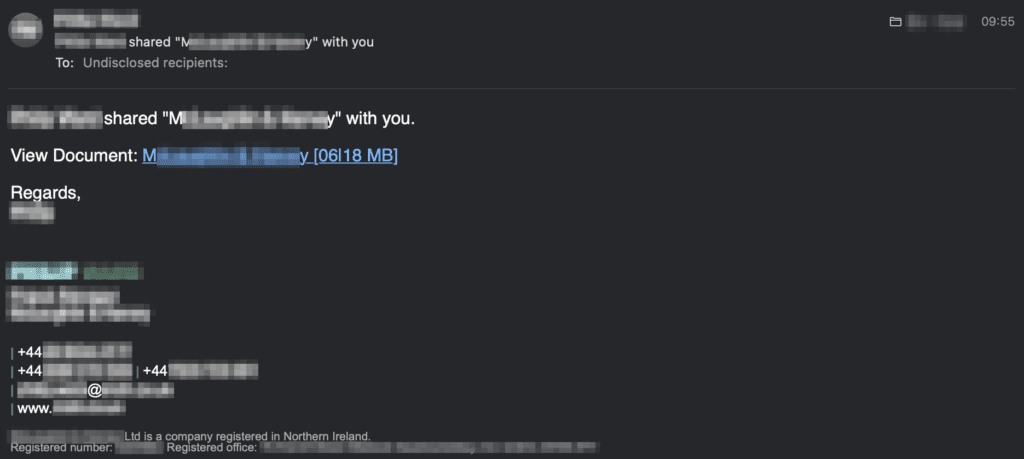
One of the phishing emails, which links to a document shared on Autodesk Drive. The sender later confirmed their account had been compromised.
As was the case in this example, victims are much more likely to click on a shared document link when the email comes from a person or business they already work with, especially when the email is furnished with the signature and other contact details they would expect to see.
The link takes the victim to a PDF document hosted on the Autodesk Drive data sharing platform. This document includes the sender’s name and the company they work for, further leveraging the trust instilled by the existing business relationship with the sender.
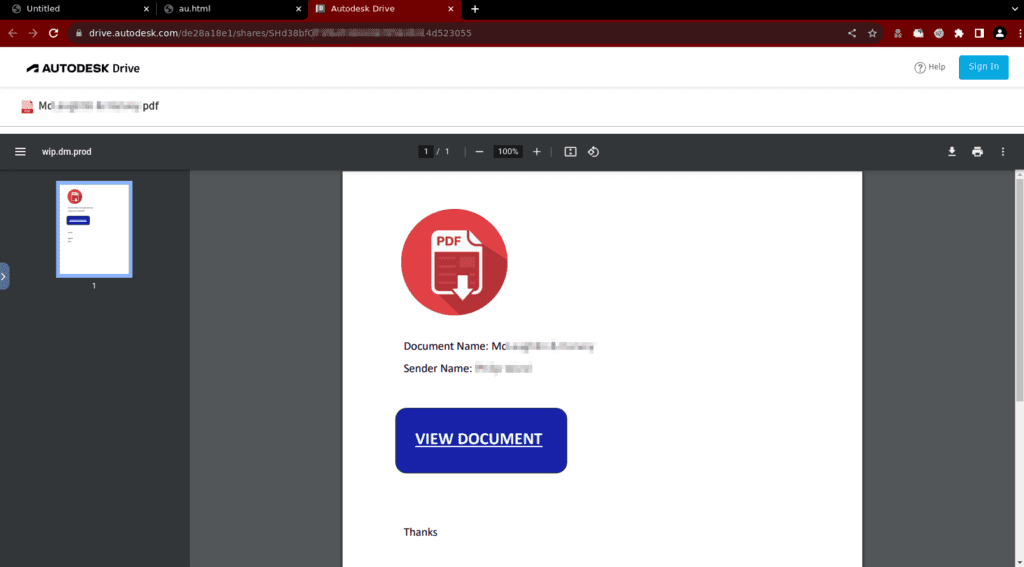
The malicious PDF file hosted on Autodesk Drive.
The links in the phishing emails use the autode.sk URL shortener, which is powered by Bitly. Autodesk Drive is intended for sharing design files in the cloud, and supports a variety of 2D and 3D data files including PDFs. It is free to use when subscribing to other Autodesk products.
When the victim clicks on the large VIEW DOCUMENT button, they will be taken to a phishing site that impersonates the Microsoft login form.
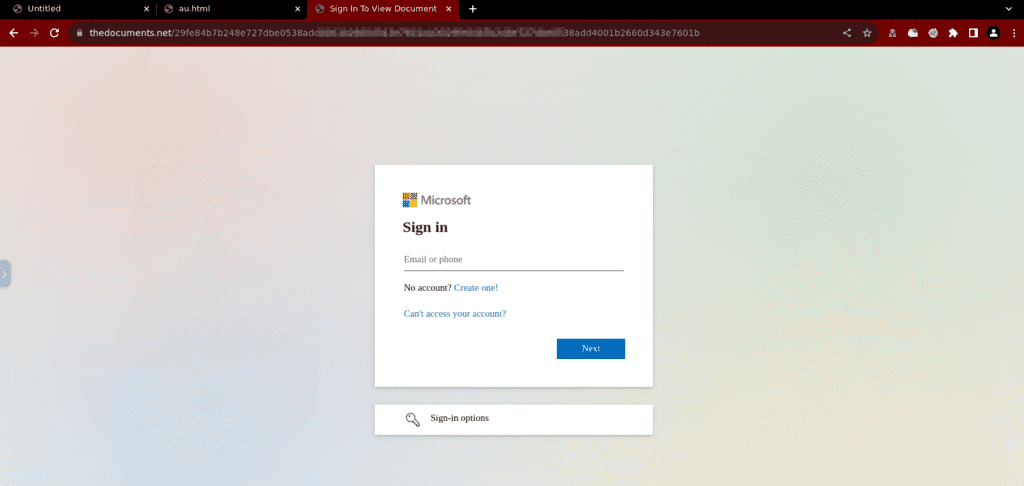
One of the spoof Microsoft login forms used in these attacks.
After entering their username and password into the spoof form, the victim is redirected to a book about real estate investment, which is hosted on Microsoft’s OneDrive service. This may give the victim the impression that this was the document they were intended to receive, possibly leaving them oblivious to the fact that their own Microsoft account has just been compromised.
The PDF copy of a book the victim will finally see.
Armed with victims’ Microsoft credentials, the criminals behind these attacks could gain unauthorised access to sensitive company data, as well as being able to send even more phishing emails from the compromised Microsoft accounts.
Another malicious PDF file hosted on Autodesk Drive. This contains different sender details and directs the victim to a different Microsoft phishing site.
These attacks also cater for different languages, which is likely automated using the locale of the sender. For example, the following PDF file on Autodesk Drive claims to have been sent by a Canadian manufacturing company in Quebec, where the official language is French.
A French version of the attack, using the language of the Canadian company it was purportedly shared by.
The scale of these attacks and the use of customised PDF documents suggests some degree of templating and automation, leading to a series of well-targeted compromises that has the potential to spread worldwide like a virus.
Businesses and employees should be on the lookout for this type of phishing attack, but its ability to spread also depends on Autodesk not hosting malicious files, and on the other infrastructure providers not hosting the Microsoft phishing sites. Netcraft provides solutions for hosting companies to prevent their internet infrastructure being abused like this. For more details, visit https://www.netcraft.com/solutions/by-industry/internet-infrastructure/.