Although many secure websites reacted promptly to the Heartbleed bug by patching OpenSSL, replacing their SSL certificates, and revoking the old certificates, some have made the critical mistake of reusing the potentially-compromised private key in the new certificate. Since the Heartbleed bug was announced on 7 April, more than 30,000 affected certificates have been revoked and reissued without changing the private key.
Internet users rely on public key cryptography to verify the identity of secure websites: SSL certificates contain a public key that is generated from its associated private key. At the start of the secure connection, the server proves that it has the private key by decrypting messages encrypted with the public key, or by cryptographically signing its own messages. Keeping the private key secret is critical — if an attacker steals the private key, he can impersonate the secure website, decrypt sensitive information, or perform a man-in-the-middle attack.
Although we typically refer to “potentially-compromised” certificates when discussing the Heartbleed bug, the CA/Browser Forum adopts a much more cautious approach to its terminology. This group lays out the Baseline Requirements for the Issuance and Management of Publicly-Trusted Certificates, and they consider a private key to be “compromised” if there exists a practical technique by which an unauthorised person may discover its value — even if there is no evidence of such a technique having been exploited.
By reusing the same private key, a site that was affected by the Heartbleed bug still faces exactly the same risks as the those that have not yet replaced their SSL certificates — if the previous certificate had been compromised, then the stolen private key can still be used to impersonate the website’s new SSL certificate, even if the old certificate has been revoked. Certificates that have been reissued with the same private key are easy to identify, as the new public key will also be identical to the old one.
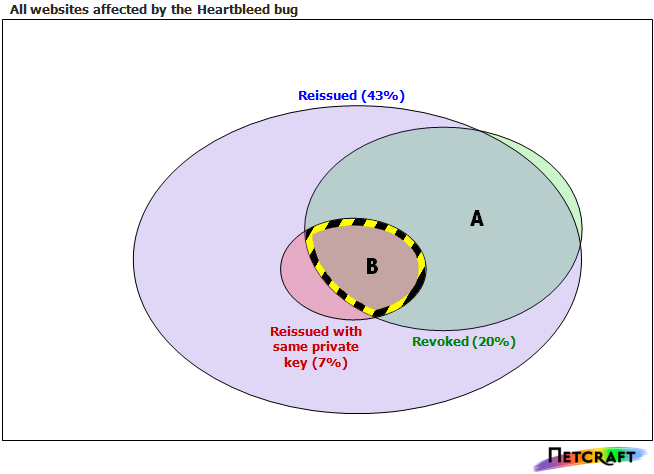
Only 14% of affected websites (Zone A in the above Euler diagram) have done all three required steps after patching the Heartbleed bug – they have replaced their SSL certificates, revoked the old ones, and made sure to use a different private key. This zone also includes sites with certificates that expired shortly after the bug was disclosed.
Zone B represents the 5% of sites that have made the fundamental mistake of reissuing their certificates without changing the private key. This is the most dangerous zone, as not only could these websites still be vulnerable to impersonation attacks, but the website administrators will probably believe that they have done everything necessary to fix the problem. An additional 2% have reused the same private key and not revoked the old SSL certificate.
The white outer zone represents nearly 57% of the affected sites which have taken no action whatsoever — they have neither reissued nor revoked their certificates. A further 21% have reissued their certificates with a new private key, but failed to revoke the old ones.
The Canadian government ought to appreciate the risks posed by the Heartbleed bug more than others, particularly after the bug was exploited to steal social insurance numbers from the Canadian Revenue Agency. However, some parts of the Canadian government have made the mistake of reusing private keys while trying to mitigate the risks.
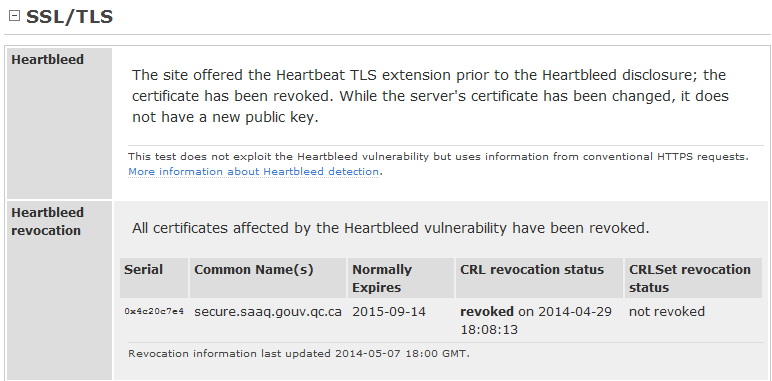
The Quebec Automobile Insurance Corporation is a crown corporation responsible for licensing drivers and providing personal injury insurance to the public. One of its websites at secure.saaq.gouv.qc.ca was issued a new SSL certificate in response to the Heartbleed bug, and the previous certificate was revoked on 29 April. The CRL revocation status listed the reason as "keyCompromise", but the issuing certificate authority nonetheless allowed the new certificate to be signed with the same private key. This means the new certificate can also be impersonated by anyone who is in possession of the compromised key.
This type of mistake could be prevented by certificate authorities: if public keys from revoked certificates were blacklisted, new requests with the same public key would be rejected. This type of automated check does not seem to be in use by most CAs; however, Netcraft’s Site Reports and browser extensions can be used to determine whether a website has signed its replacement certificate with the same private key: