Stop Threats Before They Surface
Gain critical visibility into underground criminal environments to detect and stop threats to your brand.

Early Visibility. Proactive Protection.
Our Deep and Dark Web Monitoring Capabilities
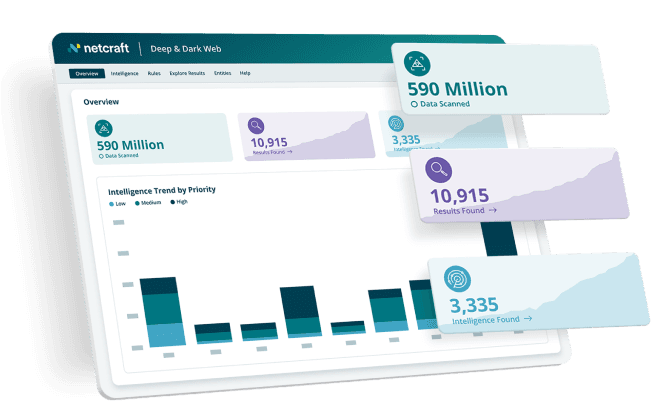
Netcraft's deep and dark web monitoring platform continuously monitors mentions of your brand, assets, and sensitive data, adding another layer of high-value threat intelligence that empowers your security teams to act fast and mitigate potential breaches, protect customer data, and outpace emerging threats.
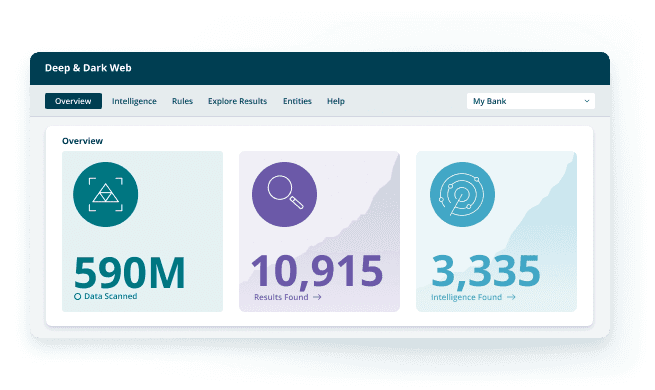
Automatically search a wide range of deep and dark web resources to find compromised information based on custom logic around your brand, aligned to the type of intelligence you want to prioritize.
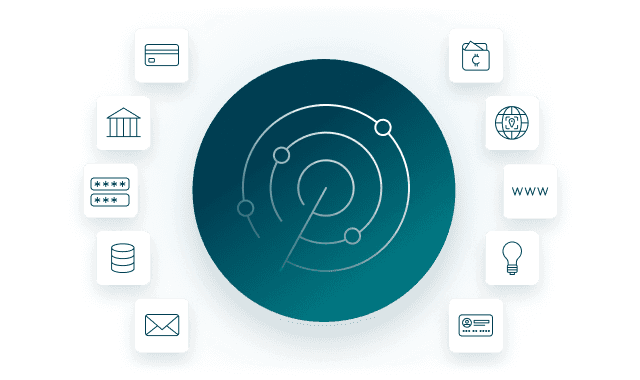
Proactively analyze and identify compromised data, including card numbers, bank account information, login credentials, API keys, email addresses, cryptocurrency addresses, phone numbers, IP addresses, Social Security numbers, National Insurance numbers, URLs, and brand, executive, and product mentions.
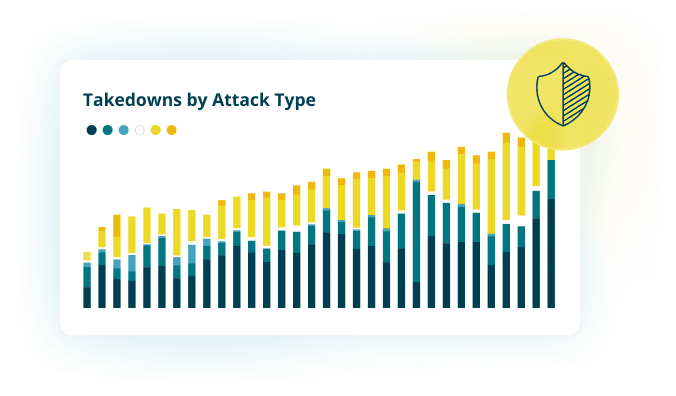
Seamlessly integrate with Netcraft Takedowns to remove stolen credentials and data when possible.
Frequently Asked Questions
What is the difference between the deep web and the dark web?
The deep web refers to parts of the internet not indexed by traditional search engines, hidden by security walls or authentication forms, such as your private email inbox, private messaging apps, online banking portals, medical records and corporate intranets. The dark web is a small, intentional subset of the deep web. It consists of encrypted websites and hidden services that require specialized software, such as the Tor Browser, to access. Common examples include illicit marketplaces and cybercriminal forums.
What is deep and dark web monitoring?
Deep and dark web monitoring is the process of scanning underground ecosystems to proactively identify emerging threats. Because cybercriminal activity often begins long before an attack is launched, continuous monitoring allows cybersecurity teams to act on these early-stage signals, preventing attacks on customers and protecting the organization's brand, sensitive data, and assets.
Deep and dark web monitoring allows organizations to move from reactive defense to proactive mitigation.
What specific channels and sources does Netcraft’s dark web monitoring cover?
Netcraft’s deep and dark web monitoring covers a diverse range of cybercriminal platforms to ensure comprehensive visibility:
Forums: Discussion-based communities (such as XSS and Exploit) used for knowledge sharing, recruitment, and trading.
Marketplaces: E-commerce style sites with vendor ratings and escrow services for selling malware and exploit kits.
Automated Vending Carts (AVCs): Fully automated underground shops (such as Russian Market) that sell stealer logs (comprehensive files harvested from infected devices containing saved passwords, browser cookies, and session tokens).
Messaging Platforms: Real-time channels like Telegram and Discord, used by groups to announce operations, share log clouds (large repositories of stolen log files), and coordinate DDoS campaigns.
What types of sensitive data can Netcraft identify on the deep and dark web?
Netcraft’s deep and dark web platform identifies critical indicators of risk, including:
Credential Exposure: Leaked credentials and infostealer logs found in forums and AVCs.
Domain and Brand Mentions: Discussions involving targeted brands, access sales linked to your infrastructure, leaked internal system information, or phishing kits impersonating your brand.
Carding and Financial Data: Compromised credit card information and trading activity within carding communities.
How does dark web monitoring integrate with Netcraft’s automated takedown services?
Unlike standard monitoring services that only provide alerts, Netcraft integrates deep and dark web monitoring with real-world disruption. When monitoring reveals early warning signals, such as phishing kits being discussed or infrastructure being deployed, Netcraft enables security teams to take immediate action. We provide the intelligence needed to trigger automated phishing takedowns and empower your team to take internal action, such as resetting compromised credentials or blocking fraudulent transactions, before an attack becomes operational.








